User Management stands as a linchpin for securing and streamlining system access across various platforms. It refers to the comprehensive process of creating, controlling, and monitoring user access to system resources, ensuring that the right individuals have appropriate permissions to perform specific tasks. By enforcing robust user management protocols, organizations not only fortify their systems against unauthorized access but also enhance operational efficiency.
Moreover, with the increasing complexity of systems and the ubiquity of multi-platform access, the importance of a robust user management system has never been more pronounced. Whether it’s granting access to a new employee, revoking privileges from a former team member, or simply monitoring user activities, effective user management ensures that system integrity remains uncompromised while delivering a seamless experience for authorized users.
Effective user management is more than just a technical necessity; it is a strategic enabler for modern organizations. By ensuring that the right individuals have the right access at the right time, businesses can safeguard sensitive data, maintain compliance, and streamline operations.
User Administration and Authentication
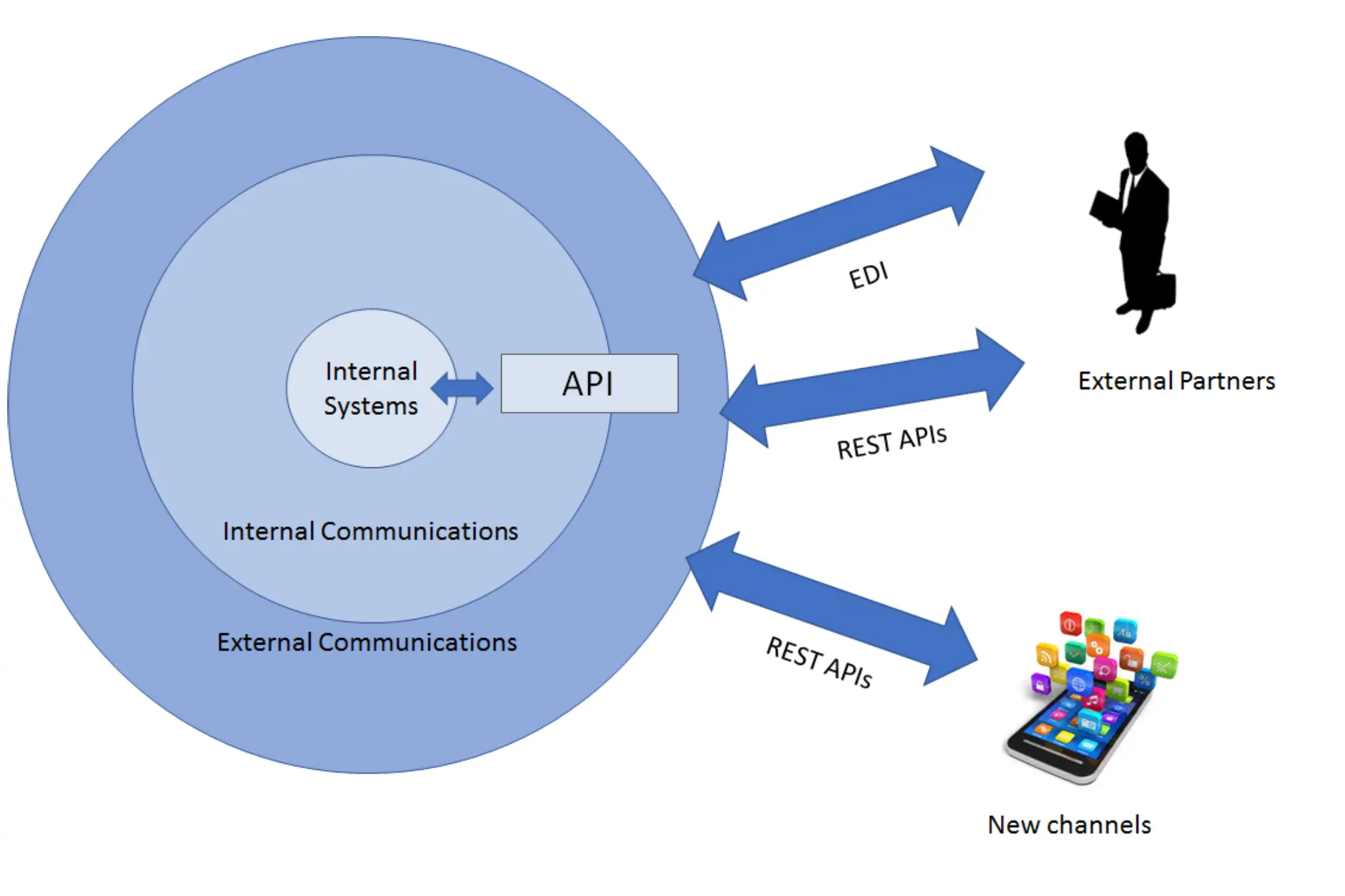
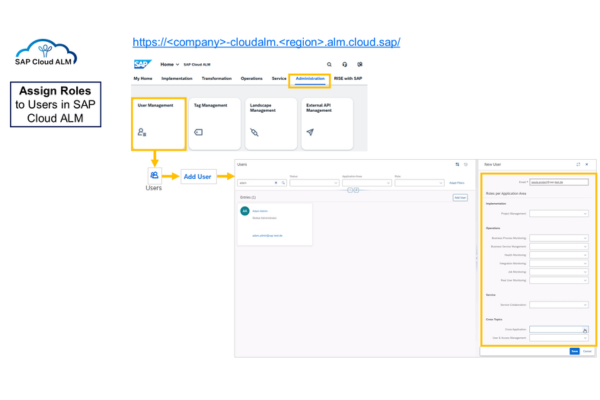
The user management in SAP Cloud ALM is divided into two components: Whereas primary identity information is stored in the connected identity provider, the user access and authorizations can be managed directly in SAP Cloud ALM.
Effective user administration is a foundational element of secure and efficient SAP operations. In modern cloud-driven landscapes, organizations must ensure that the right users have the right access at the right time—without compromising security or compliance. User Administration in SAP Cloud ALM provides a centralized and structured framework to manage users, roles, and authorizations across application lifecycle and operational processes.
As businesses scale and teams expand across regions and functions, managing access manually becomes increasingly complex. SAP Cloud ALM simplifies this process by offering role-based access control, ensuring that permissions are aligned with job responsibilities while maintaining strong governance standards.
Centralized Role and Access Management
User Administration in SAP Cloud ALM enables administrators to define and assign predefined or custom roles based on business functions. Whether a user is responsible for monitoring, implementation, project management, or operations, roles can be configured to provide access only to relevant applications and features.
This structured approach minimizes the risk of excessive authorizations while ensuring productivity. By centralizing user and role management, organizations gain clear visibility into who has access to what, strengthening overall system governance.
Secure Authentication and Identity Integration
SAP Cloud ALM integrates with identity authentication services to support secure login mechanisms. Organizations can connect their corporate identity providers to enable single sign-on (SSO), ensuring seamless yet secure user access. This reduces password management challenges while maintaining strong authentication standards.
Secure authentication mechanisms protect sensitive project data, monitoring dashboards, and operational insights from unauthorized access. Combined with role-based controls, this ensures a layered approach to security.
Governance, Compliance, and Auditability
Maintaining compliance with internal policies and regulatory requirements demands transparent user access management. SAP Cloud ALM provides traceability by logging user assignments and role changes, enabling organizations to monitor and audit access controls effectively.
Administrators can quickly review active users, adjust permissions, or remove access when roles change. This proactive governance approach reduces security risks and ensures compliance with corporate and regulatory standards.