The data illusion from fragments to one truth
The Data Illusion Nobody Talks About
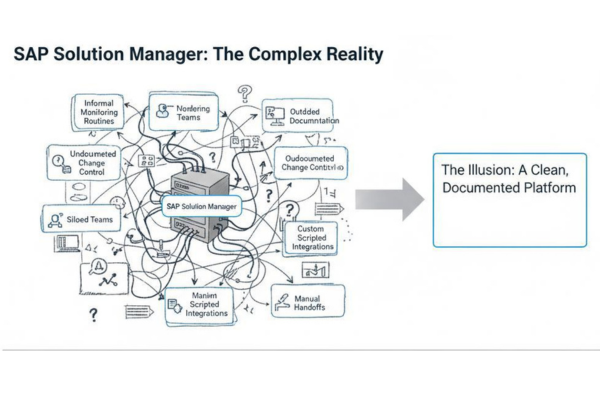
When organisations plan the transition from SAP Solution Manager to SAP Cloud ALM, the first discussion is almost always about data.
“How do we migrate it?”
“How much history do we need?”
“Can we transfer everything?”
Those are technical questions.
The strategic question is different:
Which data actually needs to survive the transition?
Over the years, Solution Manager has accumulated:
- Historical change records
- Monitoring logs
- Test documentation
- Custom workflows
- Compliance evidence
Not all of it creates value going forward.
Across multiple transitions, we have seen organisations spend disproportionate effort trying to “move everything” — only to discover later that much of the historical data is rarely accessed and poorly structured.
The real risk is not losing data.
The real risk is keeping complexity.
Selective data transfer is therefore not an IT task.
It is a governance decision.
Which audit requirements must be preserved?
Which documentation is legally required?
Which operational insights are still relevant?
Before defining migration scope, define survival criteria.
In our Controlled Replacement Model, data decisions are made after observing and stabilizing the current landscape — not before.
Because without clarity, data migration becomes data replication.
And replication is rarely transformation.
In the next post, we will look at what changes inside the organisation — and why roles matter more than tools.
Why Configuration & Security Analysis Matters
Managing configurations and security settings in a complex SAP environment is challenging. Organizations face multiple risks:
Configuration Drift:
Security Vulnerabilities:
Compliance Gaps:
Limited Visibility:
Configuration & Security Analysis addresses these challenges by providing continuous insights into system settings, enabling proactive remediation and ensuring alignment with operational and security standards.









